Businesses today need to worry about people outside their business trying to break into their network and steal their data. Unfortunately, that’s not the only direction that theft can come from. In this week’s blog, we’ll take a look at the types of technology theft you need to be aware of inside of your company and what you can do about it.
Phantom Technology Solutions Blog
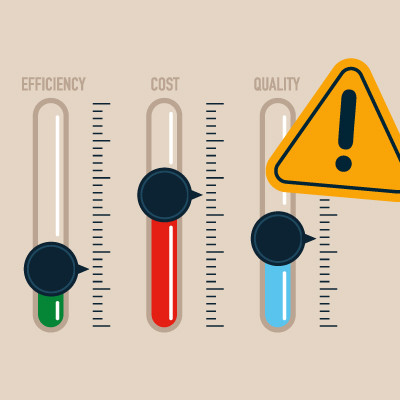
Productivity. To business owners, it can be a mantra. You can judge the success of your organization by productivity, as it often translates directly to profits. You’ll notice a lack of productivity in your operations, and potentially even your pocketbooks, so it’s incredibly important to know whether your business is being productive or not.
Technology plays a crucial role regardless of a company’s size or growth stage. Therefore, having an IT infrastructure that can adapt to changes in business scale is essential.
Let's discuss the significance of a suitable IT infrastructure and explore best practices for tailoring it to fit your business needs.
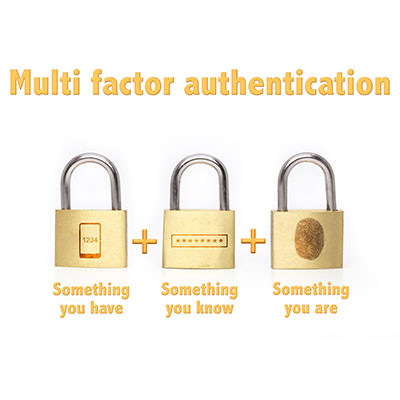
Passwords have long been a cornerstone of online account security, paired with usernames to form the basis of most login systems. Consequently, they are prime targets for hackers seeking to steal credentials and gain unauthorized access to accounts or networks. The inherent weaknesses of poor passwords have become more apparent in recent years, however. This has prompted the growing adoption of additional security measures available to users.
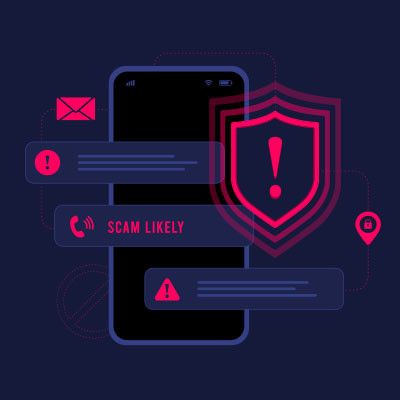
If you are a consistent reader of this blog, it will not surprise you that we think of phishing as one of the most significant threats that impact businesses today, regardless of their size or industry. Understanding this threat and implementing effective prevention measures is vital for safeguarding your organization. Let's go into how you can minimize the impact of phishing schemes and protect your business.
Regarding business logistics, inventory management is a significant contributing factor you cannot avoid. It keeps your operations running well, regardless of what type of business you run. Your company will always need its inventory, and managing it effectively and efficiently can save on costs, improve service levels, and promote overall business success.
Travel has become a common occurrence for many employees and business professionals. Yet despite the travel, their responsibilities do not get put on halt. Whether it’s for a conference, a professional development workshop, or visiting a potential client or vendor, chances are you’ll bring technology with you. It’s up to you to ensure that it is kept safe from today’s rampant cyberthreats.
How often do you struggle to talk about potential issues your business faces when you reach out to IT for help? Conversing with technicians can be especially challenging when you don’t necessarily understand the problem yourself, either. Thankfully, we have some tips to help you lead more productive conversations with your IT staff or managed service provider.
Most computers these days will come with their fair share of bloatware, i.e. unwanted software that comes preinstalled on the operating system by the developers. While the developers do tend to get paid for including bloatware with their operating systems, there is often no need for it, leading users to question why it’s there and what to do about it.
Today, we encounter situations in business where digital communication is preferred by many people, and as a result, the use of smartphones to conduct business has become more common. With this shift in the way people do business, there are several considerations that the modern worker has to navigate to properly use smartphones to their advantage. Let’s take a look at a few in today’s blog.
Network security is an incredibly nuanced topic with a lot of specifics that must be addressed. Still, today, we want to give you some actionable items that you can use to take an active role in improving network security for your business. Let’s dig into some of the essential dos and don’ts of network security for small businesses.
We’d like to extend a very Happy New Year to all of our followers! The new year is a perfect time to make resolutions, particularly for your business. Let’s look at some common areas where a resolution might prove to be an effective motivator for change within your business, as well as how you can commit to it long-term.
Scams using online retail giant Amazon have become more frequent around the holidays as online purchases tick up. Most of these scams come in the way of impersonation scams. With the holidays upon us, we thought we’d go through what kind of Amazon scams you should look for and how to avoid being a victim.
Cyberattacks are nothing to take lightly. Every year, they cause millions of dollars of damage to unprepared and unprotected businesses, which leads to many of these businesses’ failure. Let’s talk about what ultimately causes cyberattacks, so you know the kinds of situations and behaviors to keep an eye out for.
With the right technology at your side, you can ensure that your operations, productivity, and customer satisfaction are maximized. However, even with all these benefits, small businesses make mistakes, particularly in regard to the implementation process. How can your business overcome the hurdles that stem from improper technology implementation strategies? Let’s take a closer look.